The Origin: From Script to System
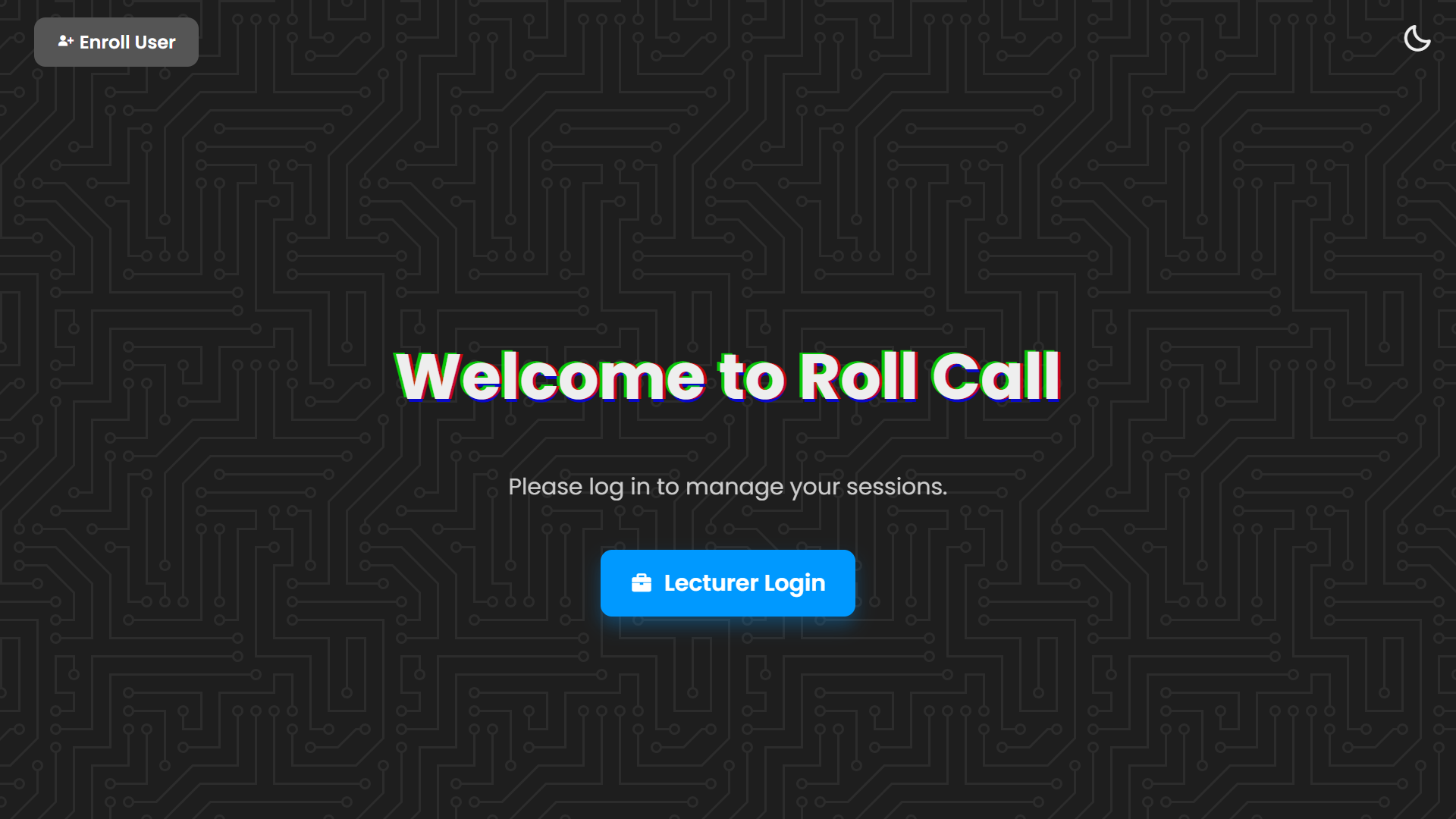
RollCall didn't start as a complex machine learning project. It started with a simple problem, some pure HTML5, and a basic QR scanner script.
I originally built the foundation as a lightweight tool to automate attendance. However, I realized that QR codes alone were easy to share and manipulate. When the opportunity for a major hackathon arose, I collaborated with Olowofela David to turn this vision into a high-security reality.
The Collaborative Division
Engineering is a team sport. By combining our skill sets, we were able to build a system that outperformed single-method competitors:
- Japheth Egbedele (My Role) – Designed the frontend architecture, the UI/UX foundation, and the Node.js orchestrator that handles dynamic QR tokenization.
- David Olowofela – Engineered the Python backend and the Computer Vision service that powers the biometric verification.
- The Result – A decoupled, Service-Oriented Architecture (SOA) that took 4th place at the hackathon and proved that collaboration scales better than working in a silo.
The Core Solution Flow
Following the blueprint from our pilot presentation, we focused on a three-stage verification pipeline:
- 1. Lecturer Auth – Facial verification required to initiate the session, ensuring only authorized personnel can open the floor.
- 2. Hybrid Scan – Primary Face Recognition with a Dynamic QR Fallback for 100% reliability even in varying environments.
- 3. Real-Time Log – Instant data entry into MongoDB Atlas, providing an audit trail that is secure and impossible to fake.
Identity Assurance Metrics
We chose to prioritize security over convenience. This meant moving away from 'fast but sloppy' algorithms in favor of mathematical precision.
| Component | Implementation | Purpose |
|---|---|---|
| Biometric Engine | ResNet-34 | Deep Metric Learning for high-accuracy matching. |
| Security Threshold | 0.4 Tolerance | Stricter than standard to eliminate 'Buddy Punching'. |
| Detection | HOG Descriptor | Reliable face location within the frame. |
Conclusion: The Post-Hackathon Audit
While RollCall secured 4th place and proved the viability of a hybrid verification pipeline, a post-build audit revealed that software-only solutions have a 'Hardware Wall.' I identified critical edge cases: the system can verify an entry, but without persistent high-fidelity cameras, it cannot prevent a student from departing immediately after, nor can standard 2D biometrics perfectly solve the 'Twin Paradox' without 3D liveness sensing.
Identifying these flaws was more valuable than the initial build. It moved the project from a 'finished application' to an ongoing research problem in physical security constraints. Neutralizing these vulnerabilities requires a transition into hardware-integrated systems—a pivot that requires a different class of infrastructure.
RollCall stands as a high-integrity prototype of what is possible with software alone. The next evolution—true 100% foolproof identity assurance—remains a strategic challenge for when the hardware catches up to the code.